Sonarqube is a quite famous tool to perform code analysis in a Continuous Integration chain.
One of the most popular post of the blog explain how to get full Unit and Integration test code coverage out of your maven build with its plugin.
Sonarqube also has a public instance of its tool, where several OpenSource projects can publish their own code analysis.
Recently also AroundTheCode Pathfinder projects has been accepted to be host on such instance, so you can view al project details on its own dashboard.
In this post I want to recap all the step to get an account on sonarqube and setup a build on travis in order to have your code automatically analyzed after the build.
The first step is to (have an OpenSource project on github and) request an account on the Sonarqube instance. As stated on the site itself:
This service is in beta version and free for Open Source projects, on invitation only. To get an invitation, please send an email to nemo AT sonarsource.com with your GitHub Account and the urls of the GitHub projects you’d like to analyze to get such invitation. Once you have it:
If your request for invitation get accepted someone from Sonarqube team will contact back by mail telling you the account has been created. Since at the moment github is the only SSO available, it will be the way you will access the site.
Once you log into your account, you have to generate an access token to get access also from TravisCi from the Security tab
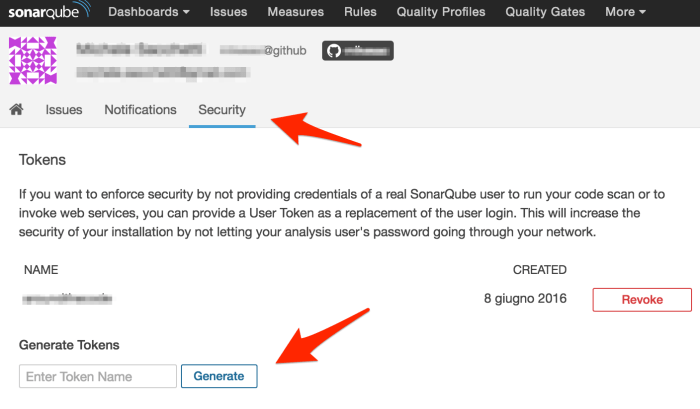
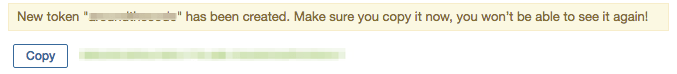
Save your token in a secure place since Sonarqube will in no way provide you again with its hash (but it’s so kind to remind it!).
Now that we have a valid token we can run our analysis from a local development environment to check everything is fine (for sonar configuration check my other post Unit and Integration tests coverage with SonarQube and Jacoco ).
mvn clean install sonar:sonar -Dsonar.host.url=https:/sonarqube.com -Dsonar.login=${SONARQUBE_TOKEN}
In this case we have stored our token in an environment variable, this will come in handy at a later stage.
Check also that your maven installation is relying on a JDK v1.8 and on the latest sonarqube maven plugin version, otherwise you could incur in some connection error toward the site:
[ERROR] Failed to execute goal org.codehaus.mojo:sonar-maven-plugin:2.7.1:sonar (default-cli) on project pathfinder: Fail to download libraries from server: javax.net.ssl.SSLHandshakeException: Remote host closed connection during handshake: SSL peer shut down incorrectly -> [Help 1]
With JDK8 and 3.x plugin declaration everything run smooth.
<pluginManagement>
<plugins>
<plugin>
<groupId>org.sonarsource.scanner.maven</groupId>
<artifactId>sonar-maven–plugin</artifactId>
<version>3.0.1</version>
</plugin>
</plugins>
</pluginManagement>
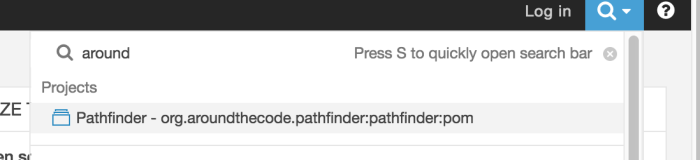
Once the analysis complete you will be able to search your project from the site interface (even if not logged in)
Now that we are sure everything is fine on Sonarqube site, we can start configuring the TravisCi build to connect and send data on every build.
Basically we need to run the very same maven string we run on the command line, but we do not want to commit our sonar token in a plain text file on our public github repository, so we will have to encode it in the .travis.yml file.
The encoding options are detailed on the travis documentation.
To encode variable you must first install travis gem on your local environment.
This will take quite long depending on your internet connection and the command will provide no output until completed, so be patient.
gem install travis
Once the installation completes, you can start encoding your variables, remember that you have to encode the full KEY=VALUE set and not just the token.
travis encrypt SONAR_TOKEN=your_sonar_token_goes_here
the output will be something like
secure : a_very_long_hash_string_here
This is the entry you must enter in the travis.yml file in behalf of your plain sonar token.
So your resulting TravisCi file should look similar to this:
cache:
directories:
– $HOME/.m2
– $HOME/.sonar/cacheenv:
secure: a_very_long_hash_string_here
jdk: oraclejdk8
language: java
script: mvn clean install sonar:sonar -Dsonar.host.url=https://sonarqube.com -Dsonar.login=$SONAR_TOKEN
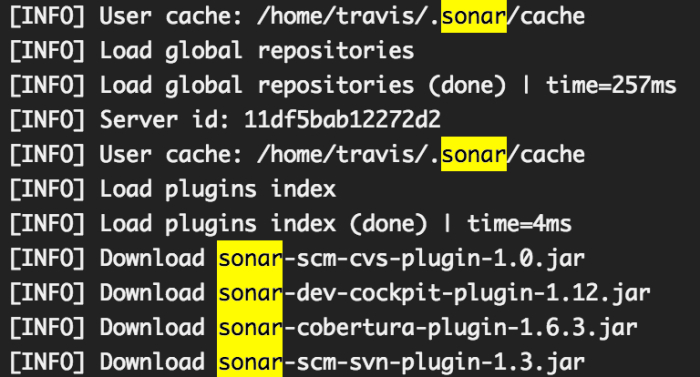
As anticipated we are forcing jdk8 usage and storing both maven and sonar cache to speedup future builds.
The build command is the very same we used in our local environment but in this case the environment variable is set in the env section with the encrypted key/value we generate.
All you have to do now is to commit your .travis.yml file and wait for travisCi to do everything for you.
You will notice a trace for the encrypted variable setting
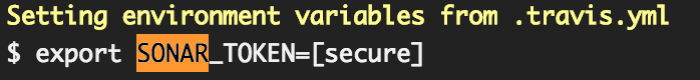
And then it will run your maven build and start sonar analysis.
Once all the download and the run has finished your will find all your data updated on the SonarQube interface


Great article! Many thanks! Please, check https://dzone.com/articles/moving-minimesos-ci-from-jenkins-to-travis for avoiding problems with Pull Request builds and for enabling reviews of Pull Requests by SonarQube